Hi Dear,
I am MOHAMED AKEES
Web & Mobile Security Specialist
TryHackMe Status

About Me
I think like an attacker — so you don’t have to. I specialize in uncovering vulnerabilities before they turn into real-world breaches. Working with startups, enterprises, and security teams, I help identify hidden weaknesses across applications, infrastructure, and systems. From bug bounty hunting to red team engagements, I turn complex security risks into clear, actionable solutions. My focus is simple: reduce attack surface, strengthen defenses, and prevent incidents before they happen. Security isn’t just about finding bugs — it’s about building resilience.
Education & Experience
Education
Experience
Skills & Tools
A comprehensive collection of technical skills, tools, and technologies I've mastered to deliver secure and efficient solutions.
 Linux
Linux
 Snort
Snort
 Sqlmap
Sqlmap
 Hydra
Hydra
 John the ripper
John the ripper
 tcpdump
tcpdump
 theHarvester
theHarvester
 Shodan
Shodan
 OpenVAS
OpenVAS
 Nessus
Nessus
 Parrot OS
Parrot OS
 Wireshark
Wireshark
 Nmap
Nmap
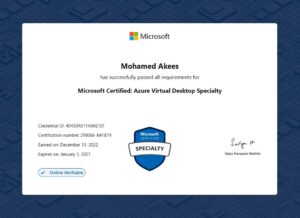
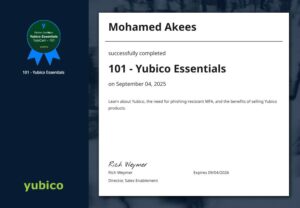
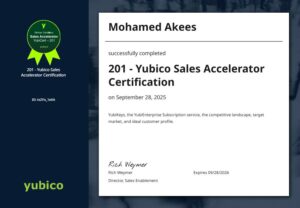
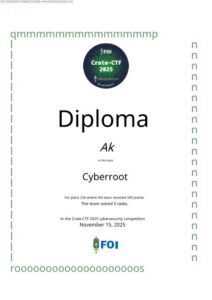
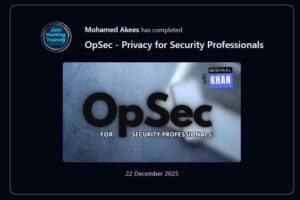
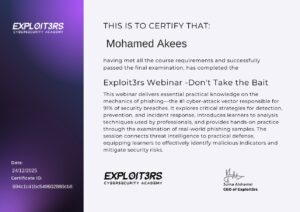
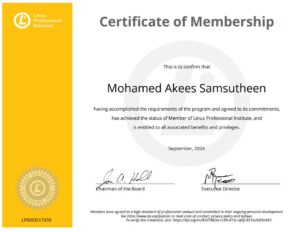
Certificates
Verified credentials and certifications that validate my expertise in cybersecurity, penetration testing, and related fields.
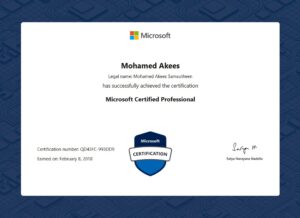
Microsoft Certified Professional
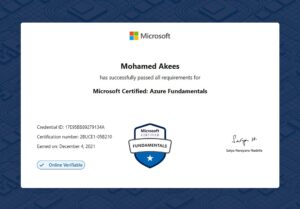
Microsoft Certified Azure Fundamentals
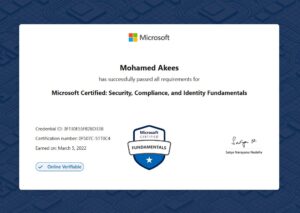
Microsoft Certified Security Compliance and Identity Fundamentals
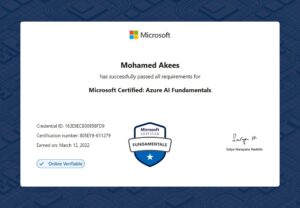
Microsoft Certified Azure AI Fundamentals
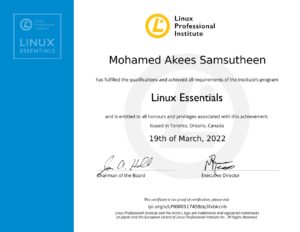
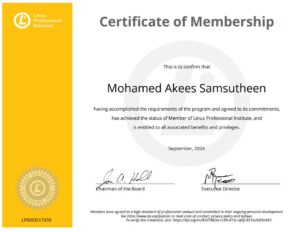
Linux Essentials
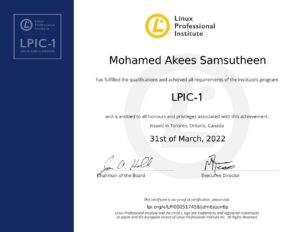
LPIC-1 Linux Administrator
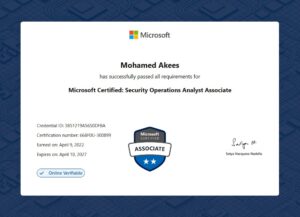
Microsoft Certified Security Operations Analyst

Pre Security Learning Path
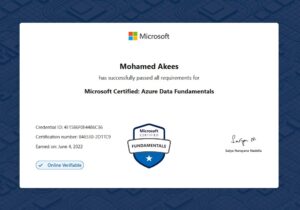
Microsoft Certified Azure Data Fundamentals
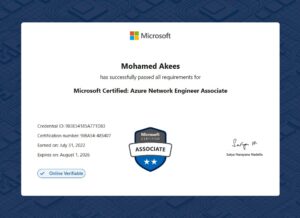
Microsoft Certified: Azure Network Engineer Associate

Microsoft Certified: Azure Database Administrator Associate
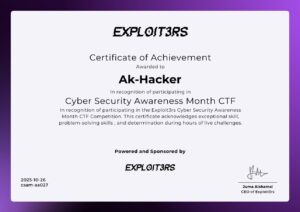
Awards & Recognitions
Notable achievements and recognition received for outstanding contributions to cybersecurity and professional excellence.
Acknowledged & Rewarded 🇺🇸
Received recognition for responsible disclosure of a security vulnerability.
Acknowledged 🇳🇱
Acknowledged for responsible reporting of a security vulnerability.
Acknowledged & Honored in Hall of Fame 🇳🇱
Recognized for responsible vulnerability disclosure.
Acknowledged 🇨🇦
Acknowledged for responsible disclosure of a security vulnerability.
Acknowledged 🇦🇺
Recognized for responsible vulnerability disclosure.
Acknowledged 🇨🇦
Acknowledged for identifying and responsibly reporting a security vulnerability.
Acknowledged & Rewarded 🇮🇳
Received recognition for responsible vulnerability disclosure.
Acknowledged 🇬🇧
Acknowledged for responsible disclosure of a security vulnerability.
Acknowledged 🇸🇬
Recognized for responsible vulnerability disclosure.
Acknowledged & Honored in Hall of Fame 🇸🇬
Recognized for responsible vulnerability disclosure.
Acknowledged & Rewarded 🇬🇧
Acknowledged for responsible vulnerability disclosure.
Acknowledged 🇱🇰
Recognized for responsible security vulnerability disclosure.
Events
Conferences, workshops, and speaking engagements where I've shared knowledge and insights with the cybersecurity community.

Ethical Hacking Awareness Program at Carmel Fatima College, Kalmunai
On 5th July 2018, we successfully conducted an Ethical Hacking Awareness Program for more than 100 students and…...

Cybersecurity & Ethical Hacking Awareness Session at Zahira College, Kalmunai
On 13th July 2018, we conducted a comprehensive Cybersecurity Awareness Program for over 30 students and teachers at…...

Cybersecurity & Ethical Hacking Awareness Program at KM-KM-AL-Manar Central College, Maruthamunai
On 4th July 2018, we conducted a Cybersecurity and Ethical Hacking Awareness Program for over 40 students and…...
Blog Posts & Articles
In-depth articles on cybersecurity trends, best practices, vulnerability research, and hands-on security solutions.
Frequently Asked Questions
Quick answers to common questions about my services, methodologies, and professional background.
Do I need a security team to work with you?
Do you work with internal security teams?
What makes your approach different?
Contact Me
Get in touch for consultations, collaborations, or inquiries about cybersecurity services and expertise.